Your Stripe secret key is sitting in a .env file pushed to GitHub. Your Shopify Admin API token is hardcoded in a Lambda function three engineers have touched this year.
If either of those sentences made you uncomfortable, it is because you already know the exposure you are carrying — and you are still not doing anything about it. IBM's 2024 data breach report puts the global average cost of a breach at $4.88 million. For a mid-market e-commerce brand doing $5M to $15M ARR, that number does not just hurt — it ends companies.
We have audited over 60 e-commerce cloud environments across the US. In 43 of those 60, at least one critical API key was exposed.
The Specific Ways Your API Keys Are Leaking Right Now
"Store keys securely" is advice everyone ignores. So let us be precise about what bad secrets management actually looks like.
A developer on your team sets up the Shippo or EasyPost shipping API key six months ago. They put it in config.js, then deployed to production. Fast forward to today — that same key has been copy-pasted into three more Lambdas, added to a Terraform variable file that got committed without a .gitignore check, and emailed to a contractor who no longer works with you. Nobody rotated it. Nobody knows how many places it lives.
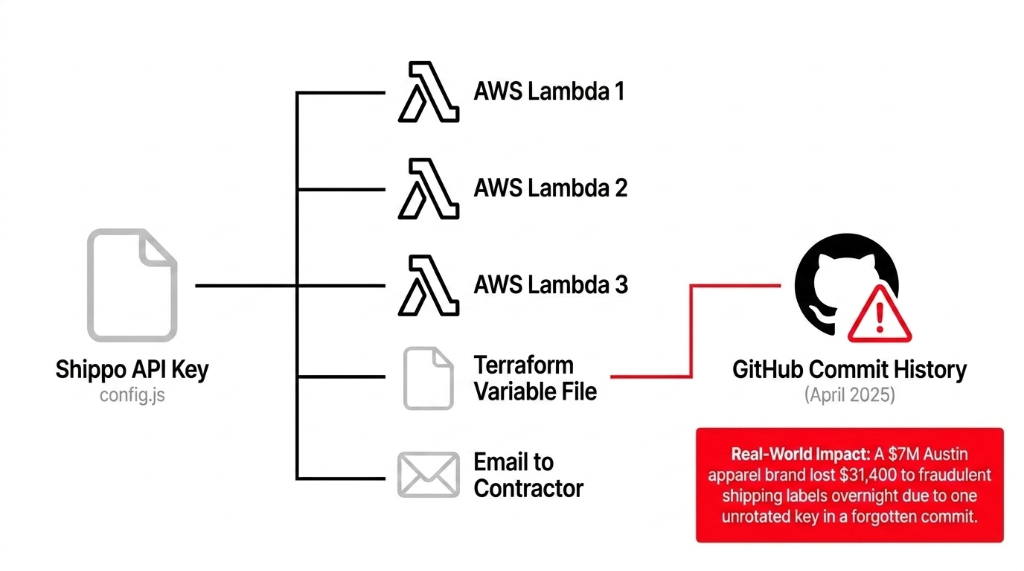
Real Damage: $7M Austin Apparel Brand
A scraper bot with credential-stuffing capabilities hit their GitHub history. Found the Shippo key in a commit from April 2025. Spun up $12,000 worth of fraudulent shipping labels overnight before the team saw the bill.
Cleanup cost: $31,400 in chargebacks, carrier fraud fees, and an emergency engineering sprint
This is not an edge case. Salt Security reports 95 to 99% of organizations with production environments experience API attacks. Your e-commerce stack likely manages between 15 and 40 live API keys at any time — Stripe, PayPal, Klaviyo, Google Shopping, ShipStation, Amazon MWS, Avalara, loyalty platforms, review widgets. Every single one of those is a door. And right now, most of those doors do not automatically lock.
Why "Just Use Environment Variables" Is the Wrong Answer
Here is the controversial opinion nobody says out loud: environment variables are not secrets management. They are secrets storage, and bad storage at that.
Every DevOps tutorial tells you to move secrets from code into environment variables. The problem? Environment variables on Lambda functions are visible to anyone with iam:GetFunction access. They do not auto-rotate. They are static strings that a misconfigured IAM policy, a compromised deploy pipeline, or a junior engineer with overly broad console access can expose in under 30 seconds.
$18,700 Lesson: The "Secured" Environment Variables
A $9M health and wellness e-commerce brand in New Jersey had "secured" their Recharge Payments API key and Gorgias API token in Lambda environment variables. An overly permissive IAM role attached to a test Lambda got exploited via a dependency vulnerability. Both keys were exposed.
$18,700 in forensic investigation, customer notification letters, and two weeks rekeying across 11 services
AWS Parameter Store is a step up — and it is free for standard parameters — but it lacks automatic rotation, native RDS/Redshift integration, and the secret versioning you need when a rotation fails mid-flight and you need to roll back within 90 seconds. (Yes, that is a real scenario during Black Friday.)
For database credentials and API keys that need automatic rotation, AWS Secrets Manager is the right tool — and at $0.40 per secret per month, the cost of protecting a Stripe live key is literally 40 cents. That is not a budget conversation. That is a priorities conversation.
How AWS Secrets Manager Actually Works for E-Commerce
Here is the operational reality, not the marketing version.
You store your secret — say, your Stripe secret key sk_live_... — in Secrets Manager with a name like prod/payments/stripe-key. AWS immediately encrypts it using AWS KMS (Key Management Service), with a unique data key per secret version. Those encryption keys never leave AWS KMS unencrypted. Even AWS employees cannot read your plaintext secret.
Runtime Secret Retrieval (Python/Boto3)
import boto3, json
client = boto3.client('secretsmanager', region_name='us-east-1')
secret = client.get_secret_value(SecretId='prod/payments/stripe-key')
api_key = json.loads(secret['SecretString'])['api_key']No hardcoding. No environment variable sprawl. The IAM role attached to your Lambda needs exactly one permission: secretsmanager:GetSecretValue on that specific secret ARN. Nothing broader.
Zero-Downtime Automatic Rotation
Here is where it gets genuinely powerful for e-commerce teams. Secrets Manager uses a 4-step Lambda rotation process that creates the new key version, registers it with the third-party service (Stripe, Shopify, etc.), tests that the new key works, then marks it current. The old version is preserved for a grace period in case any in-flight requests are still using it. Your application never goes down during rotation.
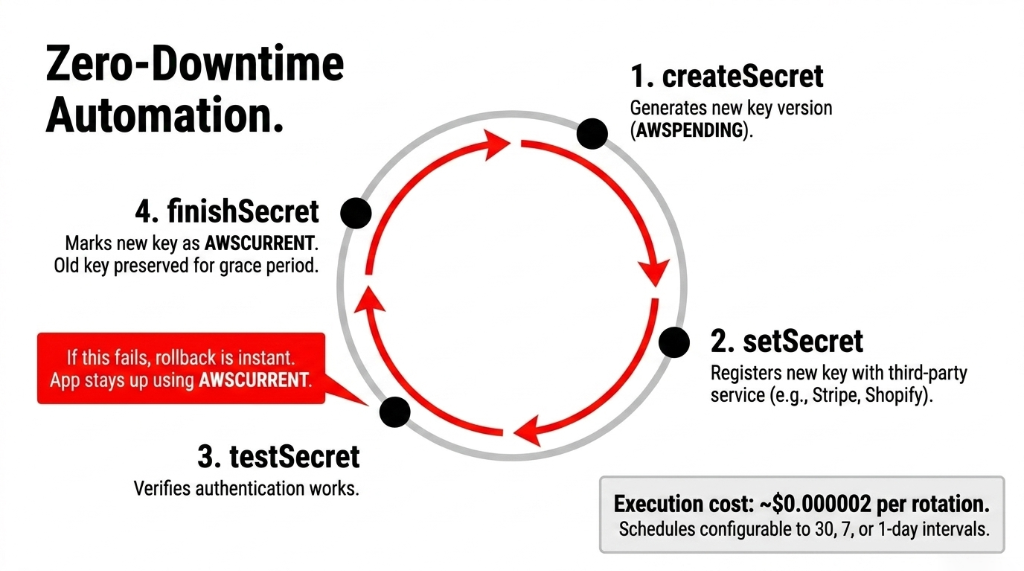
You can set rotation schedules down to every 30 days, every 7 days, or even daily. The Lambda execution cost for rotation is approximately $0.000002 per rotation — negligible to the point of irrelevance.
Setting This Up for Your E-Commerce Stack: The Real Sequence
Stop reading generic "getting started" guides. Here is the sequence that actually works for production e-commerce cloud environments.
Step 1: Inventory Every Secret You Own
Run a grep across your codebase for sk_live, pk_live, Bearer, api_key, secret, token. You will find things that scare you. The average count of exposed secrets in a $5M+ e-commerce codebase is 23 distinct credentials. Fix what you find before you build the new system.
Step 2: Create Customer-Managed KMS Keys
aws kms create-key \
--description "Secrets Manager encryption key" \
--key-usage ENCRYPT_DECRYPT \
--tags '[{"TagKey":"Purpose","TagValue":"SecretsManager"}]'Scope the key policy so only Secrets Manager can use it via kms:ViaService: secretsmanager.us-east-1.amazonaws.com. Even if someone compromises your KMS access in a different context, they cannot use the key to decrypt your secrets.
Step 3: Adopt a Strict Naming Convention
Use the format {environment}/{service}/{secret-name}:
▸ prod/payments/stripe-secret-key
▸ prod/shipping/shippo-api-key
▸ staging/email/klaviyo-private-key
IAM policies can use wildcards — prod/payments/* — granting your checkout Lambda access to all payment secrets without giving it access to email platform keys. Without naming conventions, you end up with stripe-key-prod-v2-final-USE-THIS-ONE and your IAM policies become * because nobody wants to maintain specificity in chaos.
Step 4: Use VPC Endpoints for Secrets Manager
If your application runs inside a VPC (and it should), create a com.amazonaws.us-east-1.secretsmanager VPC endpoint. Secret retrieval traffic never leaves AWS's private network. No internet gateway. No exposure to traffic interception.
Step 5: Enable CloudTrail Logging
Every GetSecretValue, RotateSecret, and DeleteSecret call gets logged. Set up a CloudWatch Alarm for GetSecretValue calls from outside expected IAM roles or outside business hours. That alarm costs $0.10/month and has a real chance of catching a breach in under 15 minutes.
The Numbers You Should Be Tracking After Go-Live
Post-Implementation Metrics
100% Rotation Coverage
All production keys on automated rotation within 30 days of implementation. A $8M Dallas electronics brand hit 94% coverage in 11 days.
10-40ms Retrieval Latency
With SDK caching enabled at 5-minute TTL. 100 concurrent Lambdas do not each make a separate API call — use aws-secretsmanager-caching.
$6.80 to $10.00/Month
17 to 25 secrets at $0.40 each, plus ~$2.50 for 500,000 monthly retrievals at $0.05 per 10,000 API calls. Total: under $13/month for enterprise-grade protection.
80% Breach Reduction
Per Verizon DBIR: 80% of data breaches are caused by mismanaged secrets. Automated rotation and centralized access control directly address that 80%.
Multi-Region Replication: What Black Friday Actually Demands
Here is the insider detail that most AWS blog posts skip: if your e-commerce store runs in a single region (us-east-1), a regional Secrets Manager outage during peak traffic means your checkout flow cannot retrieve the Stripe key and returns a 500 error.
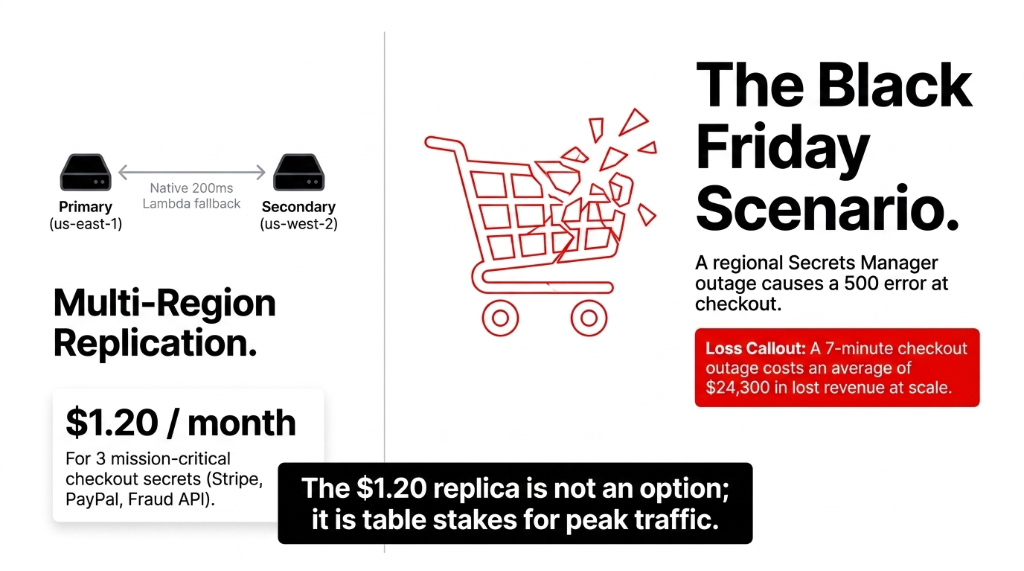
Secrets Manager supports multi-region secret replication to secondary regions like us-west-2. You pay $0.40/month for each replica secret. For your Stripe live key, your PayPal credentials, and your fraud prevention API token — the three secrets that directly touch checkout — $1.20/month in replication cost is not a decision. It is table stakes.
Configure your application to attempt retrieval from the primary region first, fall back to the replica region within 200ms if the primary returns a timeout. If you are running $500,000/day in transactions on Black Friday and checkout goes down for 7 minutes due to a regional issue, you have lost approximately $24,300. The $1.20 replica is not the expensive option.
Secrets Manager vs. Parameter Store: Stop Defaulting to Free
We hear this objection constantly: "We are already using SSM Parameter Store — it is free." Correct. And for non-sensitive configuration — feature flags, timeout values, app config strings — it is the right call. But here is the trade-off:
| Capability | SSM Parameter Store (Standard) | AWS Secrets Manager |
|---|---|---|
| Storage cost | Free | $0.40/secret/month |
| Automatic rotation | No | Yes (built-in) |
| Native RDS/Redshift integration | No | Yes |
| Secret versioning + rollback | Limited | Full version history |
| Cross-region replication | No | Yes |
| Zero-downtime rotation | No | 4-step Lambda process |
For Shopify Admin API tokens, Stripe secret keys, PayPal client secrets, and Klaviyo private API keys — use Secrets Manager. For your store's theme color config or checkout timeout setting — use Parameter Store. Do not mix this up.
Frequently Asked Questions
Does AWS Secrets Manager work with Shopify's API?
Yes. You store your Shopify Admin API token in Secrets Manager under a name like prod/shopify/admin-api-key, then retrieve it at runtime via the SDK in your Lambda or ECS service. Shopify does not natively support automatic credential rotation, so you use a custom Lambda rotation function to generate a new token via the Shopify Partner API and update the secret programmatically.
How much does AWS Secrets Manager cost for a typical e-commerce store?
At $0.40 per secret per month plus $0.05 per 10,000 API calls, a store managing 20 API keys costs roughly $8 to $10/month in secret storage. At 500,000 monthly retrievals, API call costs add approximately $2.50. Total: under $13/month for enterprise-grade secret protection on your entire credentials stack.
Is AWS Secrets Manager PCI-DSS compliant for payment API keys?
Yes. AWS Secrets Manager is included in AWS PCI-DSS Level 1 certification. Secrets are encrypted with AES-256 via AWS KMS, access is controlled through IAM policies with full CloudTrail audit logging, and rotation capabilities directly support PCI-DSS Requirement 8 for credential management. You still own your own IAM configuration — compliance requires correct setup, not just the service.
What happens if secret rotation fails mid-process?
Secrets Manager preserves both the AWSCURRENT (old) version and the AWSPENDING (new) version during the rotation window. If the testSecret step fails — meaning the new key does not authenticate correctly — Secrets Manager does not promote the new version to current. Your application continues using the old key without interruption. The failed rotation triggers a CloudWatch event you should route to your alert system.
Can multiple AWS Lambda functions access the same secret?
Yes. Attach an IAM policy to each Lambda execution role granting secretsmanager:GetSecretValue on the specific secret ARN. Use the Secrets Manager SDK built-in caching layer (aws-secretsmanager-caching) with a 5-minute TTL so 100 concurrent Lambda invocations do not each make a separate API call — that would turn $0.05 per 10,000 calls into a measurable line item at scale.
Stop Bleeding Cash on Preventable Security Incidents
Run a grep on your codebase right now for sk_live and api_key. If results come back from anything other than a Secrets Manager retrieval call, you have exposure. We will identify your highest-risk secrets, map your IAM permission gaps, and show you exactly what a $4.88M breach scenario looks like for your specific stack — in the first call. No pitch deck. No fluff.
Free audit. Exposed secrets identified. IAM gaps mapped on the first call.

