Right now — at 2:17 AM on a Tuesday — someone is harvesting your customers' payment data.
Your Shopify store is running on AWS. Orders are flowing. Conversion rate looks healthy. And a bad actor is quietly exfiltrating customer records from a compromised EC2 instance. You will not know until Monday morning when your payment processor freezes your account.
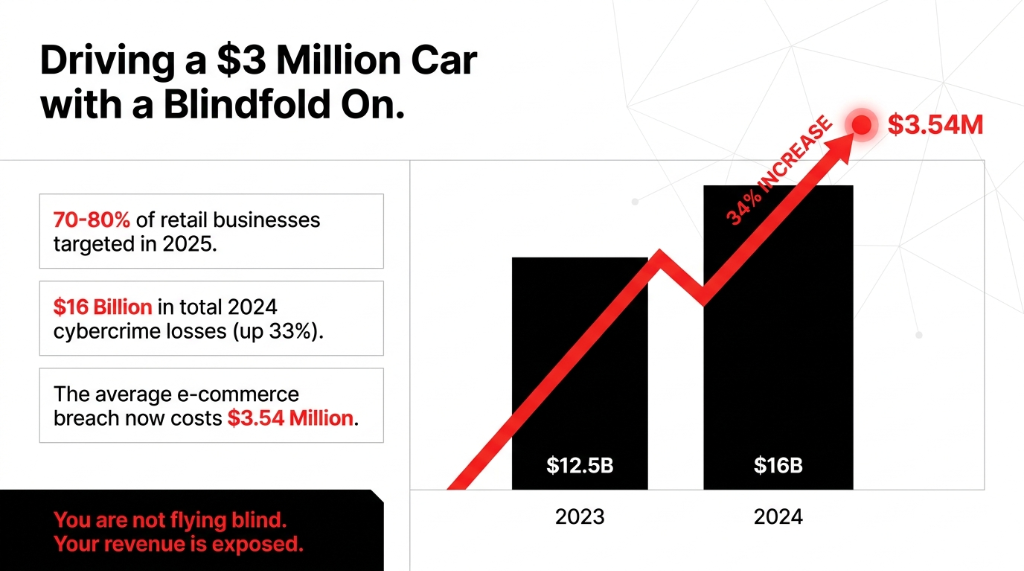
That is not a hypothetical. Retail cyber attacks increased 34% in 2025. The average e-commerce breach now costs $3.54 million per incident.
If your AWS stack does not have GuardDuty running, you are not flying blind. You are driving a $3 million car with a blindfold on.
Why E-Commerce Is the Attacker's Favorite Target
The U.S. retail sector is the most frequently targeted by cybercriminals globally. Between 70% and 80% of retail businesses reported facing cyber attacks in 2025 alone. And here is the ugly truth nobody in the "cybersecurity awareness" space will say out loud: most e-commerce brands running AWS think their cloud provider handles security for them.
They don't.
AWS operates under a Shared Responsibility Model. AWS secures the infrastructure. You secure everything that runs on it — your EC2 instances, your S3 buckets full of customer data, your Lambda functions, your RDS databases holding 400,000 order records. When a credential gets compromised and an attacker starts exfiltrating data from your S3 bucket at 11 PM, AWS will not stop it. That is your job.
The Numbers That Should Terrify You
$16 Billion
FBI IC3-reported cybercrime losses in 2024 — a 33% jump from $12.5 billion in 2023. E-commerce absorbs a meaningful chunk.
65% Phishing
Phishing accounts for 65% of retail attack vectors. Your developer gets one bad email, and your AWS console credentials are gone.
Only 33% Protected
Only 33% of retail businesses have deployed advanced cybersecurity tooling. The rest are hoping nobody notices.
What GuardDuty Actually Watches (and Most Blogs Will Not Tell You)
Most articles describe GuardDuty as a "threat detection service." That tells you nothing useful. Here is what it actually monitors for an e-commerce stack — 7 telemetry sources, all analyzed out-of-band with zero latency impact on your live traffic:
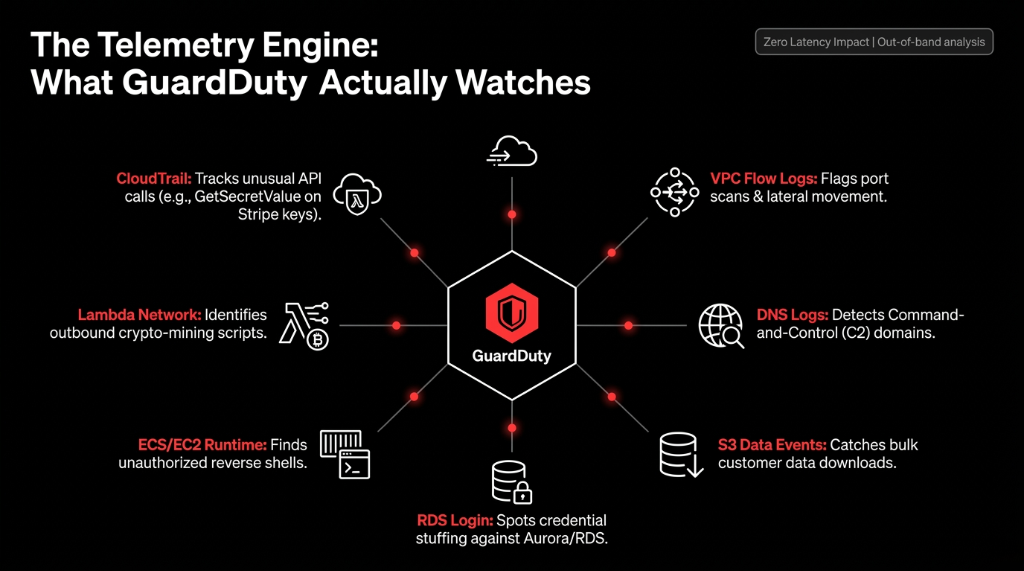
CloudTrail Management Events
Every API call in your AWS account — including when someone calls GetSecretValue on your Stripe API keys at 3 AM from an IP in Eastern Europe.
VPC Flow Logs
Network traffic in and out of your instances. Catches port scans, data exfiltration to unknown IPs, and lateral movement between your app and database servers.
DNS Query Logs
Flags when your EC2 instance starts resolving known command-and-control (C2) domains — a telltale sign of malware.
S3 Data Events
Catches when someone bulk-downloads your entire customer database — all 2.3 million records — in a single API call.
RDS Login Activity
Monitors for credential stuffing attacks against your Aurora or RDS databases. 80,000 login attempts over 72 hours? GuardDuty catches that pattern.
ECS/EC2 Runtime Monitoring
Process-level telemetry. Knows when a container that should only be running your Next.js storefront suddenly spawns a reverse shell.
Lambda Network Activity
Monitors outbound connections from your serverless functions. Catches crypto-mining scripts injected via a vulnerable npm package calling 185.220.101.47.
We have seen clients run Shopify storefronts on AWS with open S3 bucket policies because someone set them up fast before a product launch and never locked them down. GuardDuty would catch that exposure and alert on the first suspicious access within minutes. Without it, that bucket stays open until a researcher — or an attacker — finds it.
Extended Threat Detection: The Part That Changes Everything
Here is what AWS released at re:Invent 2024 that most e-commerce teams still have not deployed: GuardDuty Extended Threat Detection.
Standard threat detection catches individual events. Someone failed to log in 50 times? Alert. Unusual API call? Alert. The problem is that sophisticated attackers do not trip single-event rules. They move slowly, across multiple services, over days or weeks.
How Extended Threat Detection Chains Signals
Extended Threat Detection uses AI and machine learning at AWS scale to correlate signals across multiple data sources over extended time periods. It chains what looks like unrelated events:
Day 1: Slightly unusual IAM role assumption
Day 4: New outbound network destination
Day 9: Bulk S3 GetObject call on customer data
Result: Single critical-severity finding with full attack timeline and MITRE ATT&CK mapping
In December 2025, AWS expanded this to EC2 and ECS workloads — introducing AttackSequence:EC2/CompromisedInstanceGroup and AttackSequence:ECS/CompromisedCluster. For an e-commerce platform running containerized microservices on ECS — your cart service, your inventory sync, your payment processor webhook handler — this means GuardDuty can identify when a single compromised container is being used as a launchpad to move laterally through your entire cloud infrastructure.
Each finding comes with MITRE ATT&CK tactic mapping and specific remediation steps. Your security team does not have to spend 4 hours figuring out what happened. They get a summary, a timeline, and a to-do list. That cuts your Mean Time to Respond (MTTR) from hours to minutes.
The 5 Attack Patterns That Kill E-Commerce Stores
Generic "threat detection" language does not help you prioritize. Here are the exact patterns GuardDuty stops — named, with specifics:
1. Credential Compromise to Data Exfiltration
An attacker phishes one of your developers, gets their AWS console credentials, assumes an IAM role, and starts downloading your RDS customer export from S3. Extended Threat Detection catches this as a chained sequence, not two separate low-priority alerts.
2. Cryptojacking via Compromised EC2
A misconfigured security group leaves port 22 open. An attacker gets in, installs a crypto miner, and your EC2 bill goes from $4,200/month to $31,000 in 18 days. Runtime Monitoring sees the unauthorized process execution and fires a critical alert before you get the billing shock.
3. Supply Chain Attacks via Lambda
Your storefront uses 14 third-party npm packages in Lambda functions. One gets compromised upstream. GuardDuty Lambda Network Activity Monitoring sees the function making outbound calls to an unknown IP at 185.220.101.47 — and flags it immediately.
4. RDS Credential Stuffing
Attackers run 80,000 login attempts against your Aurora database over 72 hours using credentials leaked from a third-party breach. GuardDuty RDS Protection detects the anomalous login pattern and alerts before a single account is compromised.
5. Insider Threat — Bulk Customer Data Export
A disgruntled employee with S3 read access downloads your entire customer CSV before their last day. GuardDuty S3 Protection flags the unusual volume and access pattern within minutes. (Yes, this happens more often than you think.)
How to Deploy GuardDuty for an E-Commerce AWS Stack
This is the part most blogs skip because it requires actual operational knowledge. Here is the 6-step deployment we run for every AWS e-commerce client:
Step 1: Enable GuardDuty Across ALL Regions
Not just us-east-1 where your main stack lives. Attackers specifically probe undermonitored regions to establish footholds. Takes 3 minutes in the AWS console. Enable it everywhere.
Step 2: Turn On All Protection Plans
▸ S3 Protection — mandatory if you store customer data or product assets
▸ RDS Protection — mandatory if you run Aurora or RDS
▸ EKS or ECS Runtime Monitoring — mandatory for containers
▸ Lambda Protection — mandatory for serverless storefronts
▸ Malware Protection for EC2 — catches injected malware on application servers
Step 3: Set Up a GuardDuty Administrator Account
If you run multiple AWS accounts — separate for prod, staging, data analytics, and dev — centralize GuardDuty findings into a single administrator account. One unified threat dashboard instead of logging into 4 accounts to chase alerts.
Step 4: Route Findings to Your SIEM or Slack
GuardDuty findings flow into Amazon EventBridge. Route critical-severity findings to PagerDuty, Slack #security-alerts, or your SIEM (Splunk, Datadog) in under 10 minutes of configuration. Do not let critical findings sit in a console tab nobody checks.
Step 5: Add Custom Threat Lists
As of September 2025, GuardDuty supports custom entity lists — your own domain and IP blocklists. If you know specific IPs that scrape your pricing data or fraudulent accounts that hit your checkout, feed those directly into GuardDuty's detection engine.
Step 6: Use the 30-Day Free Trial
AWS gives you a full 30-day free trial with estimated cost projections. You will see exactly what your monthly bill will be before you commit. For a mid-size store processing 500 GB/month in logs, foundational detection starts at $1.00 per GB for the first 500 GB — roughly $500/month. Compare that to $3.54 million per breach.
What GuardDuty Does NOT Do (Be Honest With Yourself)
GuardDuty is a detection tool. It does not block traffic. It does not remediate. It does not replace AWS WAF (which blocks malicious HTTP requests), AWS Shield (which handles DDoS), or AWS Security Hub (which aggregates findings from multiple security services).
| Layer | Tool | What It Does |
|---|---|---|
| Perimeter | AWS WAF + Shield | Blocks bad HTTP requests, DDoS |
| Detection | AWS GuardDuty | Identifies threats across your AWS account |
| Compliance | AWS Security Hub | Aggregates and scores your security posture |
| Secrets | AWS Secrets Manager | Keeps Stripe keys, DB passwords out of your code |
| Encryption | AWS KMS | Encrypts customer PII at rest |
| Remediation | Lambda + EventBridge | Auto-isolates compromised resources on GuardDuty alert |
GuardDuty is the brain that sees the threat. The rest of the stack is what actually enforces the response. Deploy them together.
The Real Cost Math (Stop Making Excuses)
Frankly, the pricing objection we hear from e-commerce founders is the most expensive mistake they make.
GuardDuty Pricing for a $4M ARR Storefront
Foundational Detection
~800 GB/month in CloudTrail, VPC Flow, and DNS logs. Approximately $625/month at tiered pricing.
Runtime Monitoring
20 ECS task vCPUs. Adds another $30/month for process-level visibility into container workloads.
Total: Under $660/month
AI-driven threat detection across your entire cloud environment. One ransomware incident — average dwell time 197 days without GuardDuty — costs $3.54 million.
448 Years of Coverage
$3.54 million divided by $660/month = 5,363 months = 448 years of GuardDuty coverage. The math is not close. It is not even in the same zip code.
AWS gives you a full 30-day free trial with cost projections. You will know exactly what you owe before you commit a single dollar.
We Have Seen What Happens Without It
We work with D2C brands running AWS across the US, and we see the same pattern repeatedly: companies invest heavily in performance optimization — CloudFront CDN, RDS read replicas, auto-scaling groups — and spend zero on security visibility.
Braincuber's cloud infrastructure practice includes GuardDuty deployment as a non-negotiable baseline for every AWS engagement. We configure multi-account GuardDuty centralization, build EventBridge to Slack/PagerDuty pipelines for instant alerting, and integrate findings into Datadog or Splunk for brands that already have a SIEM.
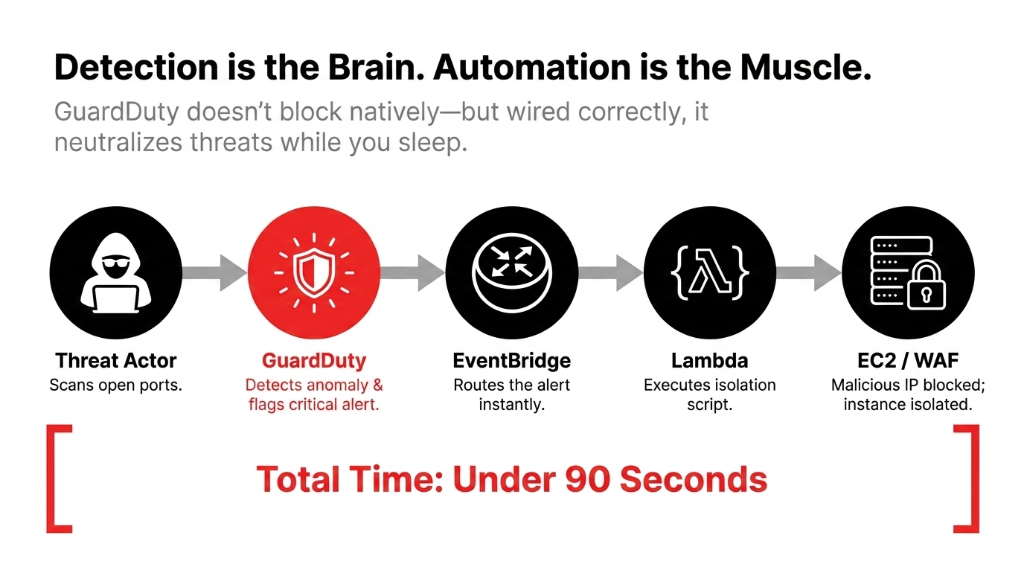
We also automate remediation: when GuardDuty fires a critical alert for a compromised EC2 instance, our Lambda automation isolates it in the security group within 90 seconds — before any human wakes up and checks their phone.
Frequently Asked Questions
Does AWS GuardDuty work without any agents installed?
Yes. GuardDuty foundational threat detection — covering CloudTrail, VPC Flow Logs, and DNS logs — requires zero agent installation and zero infrastructure changes. Runtime Monitoring for EC2 and ECS does deploy a lightweight agent for process-level telemetry, but foundational coverage starts immediately after a single click to enable the service.
How much does AWS GuardDuty cost for a mid-size e-commerce store?
For a store generating 500 GB/month in logs, foundational detection costs approximately $500/month at $1.00 per GB. Adding Runtime Monitoring for 100 vCPUs adds $150/month. Total ballpark: $650 to $900/month depending on your stack size, with a full 30-day free trial available before any charges apply.
Can GuardDuty detect fraud or fake orders on my Shopify store?
GuardDuty detects infrastructure-level threats — compromised credentials, unusual API calls, data exfiltration — not application-level fraud like fake orders. For checkout fraud, pair GuardDuty with AWS Fraud Detector or Signifyd. GuardDuty protects your AWS backend, not your checkout flow.
Will GuardDuty slow down my AWS infrastructure or increase latency?
No. GuardDuty analyzes logs and data streams out-of-band — it reads copies of your logs, not your live traffic. There is zero impact on application performance, latency, or throughput. It operates entirely outside your critical path.
Does GuardDuty automatically block threats or just detect them?
GuardDuty detects and alerts — it does not block automatically. However, you can wire findings to AWS EventBridge, which triggers Lambda functions to auto-remediate: isolating a compromised EC2 instance, revoking a suspicious IAM credential, or blocking a malicious IP in AWS WAF — all within seconds of a critical finding.
Your Store Is Either Monitored or It Is a Target
If you are running an e-commerce stack on AWS without GuardDuty configured properly, you are gambling $3.54 million on nobody noticing. We will show you exactly what is exposed on the first call.
Free audit. GuardDuty config reviewed. Exposed attack surfaces identified on the first call.

