What This Mapping Guide Covers
1. The timeline nobody told you about — and why "future-dated" was a trap
2. v3.2.1 vs. v4.0 side-by-side: 8 control areas with direct operational impact
3. The 6 requirements where organizations are failing right now
4. Real case studies: hospitality (3,500 devices), financial services (58% breach reduction)
5. The 30-day accelerated mapping path (not the 6-month QSA billable hours version)
The Story Nobody Told You About v4.0
PCI-DSS v4.0 was published by the PCI Security Standards Council in March 2022. Organizations were given until March 31, 2024, to retire v3.2.1, and then a further 12-month runway — until March 31, 2025 — to implement the new requirements tagged "future-dated."
Here is what most compliance consultants glossed over: the phrase "future-dated" lulled a lot of teams into a false sense of time. The requirements weren't optional suggestions. They were scheduled obligations, the same way your tax filing deadline is "future-dated" until it isn't.
PCI DSS v4.0.1 replaced v4.0 as the active standard on December 31, 2024, incorporating minor clarifications — but zero new or deleted requirements. So if someone on your team is telling you "they updated it again, let's wait," that is a stall tactic, not a strategy.
What Actually Changed: v3.2.1 vs. v4.0 Side by Side
Stop reading the marketing summaries. Here is the direct operational impact:
| Control Area | v3.2.1 Reality | v4.0 Mandate | Your Gap Risk |
|---|---|---|---|
| MFA Coverage | Remote CDE access only | ALL CDE access, including local console | On-prem login without MFA = violation |
| Monitoring | Annual/periodic checks | Continuous monitoring required | Quarterly log review = non-compliant |
| Encryption | TLS 1.0/1.1 with compensating controls | TLS 1.2 min, TLS 1.3 recommended; full cert inventory | Expired SSL certs = instant finding |
| Vuln Scanning | Critical vulnerabilities only | All vulns, authenticated scans, more frequent | Qualys profile ignoring medium CVEs won't pass |
| Email Security | Not required | DMARC enforcement mandatory (reject policy) | p=none DMARC = fail Req 5.4.1 |
| Password Policy | 7-char min, periodic change | Longer, complex; weak credential monitoring | AD default policies probably fail |
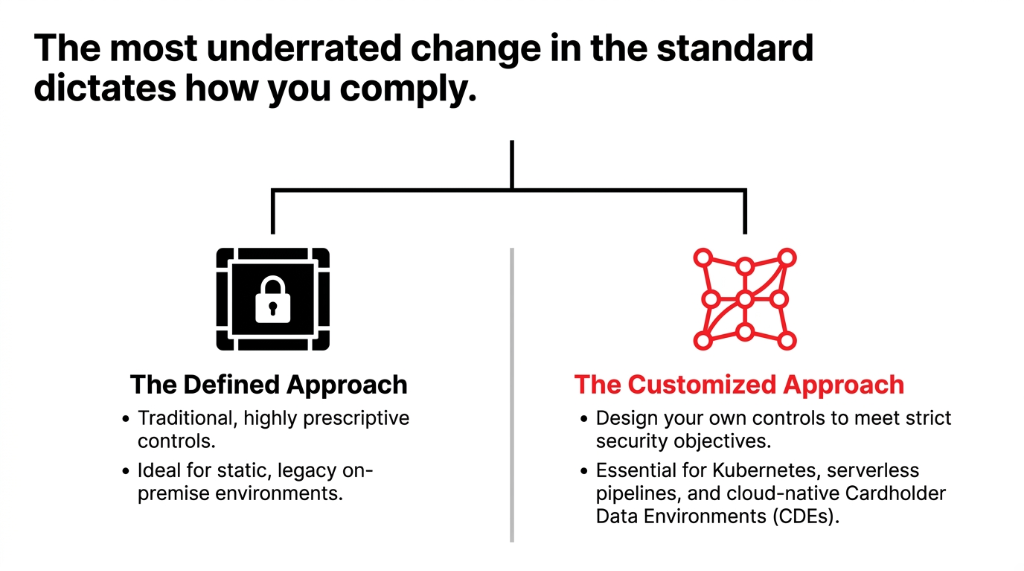
| Compliance Approach | Defined (prescriptive only) | Defined OR Customized approach | First time you can tailor controls to your architecture |
| Scope Definition | Static, requirement-driven | Dynamic; includes containers, serverless | Cloud-native CDE needs full re-scope |
The 6 Requirements Where Most Organizations Are Failing Right Now
We are not listing all 64. What we are telling you is where the gaps are showing up repeatedly in real assessments:
1. Requirement 8.4.2 — MFA Everywhere in the CDE
Not just VPN. Not just admin accounts. Every user. Every access path. Every time. If your developers can SSH into a payment processing server from a local machine without MFA, that is a finding.
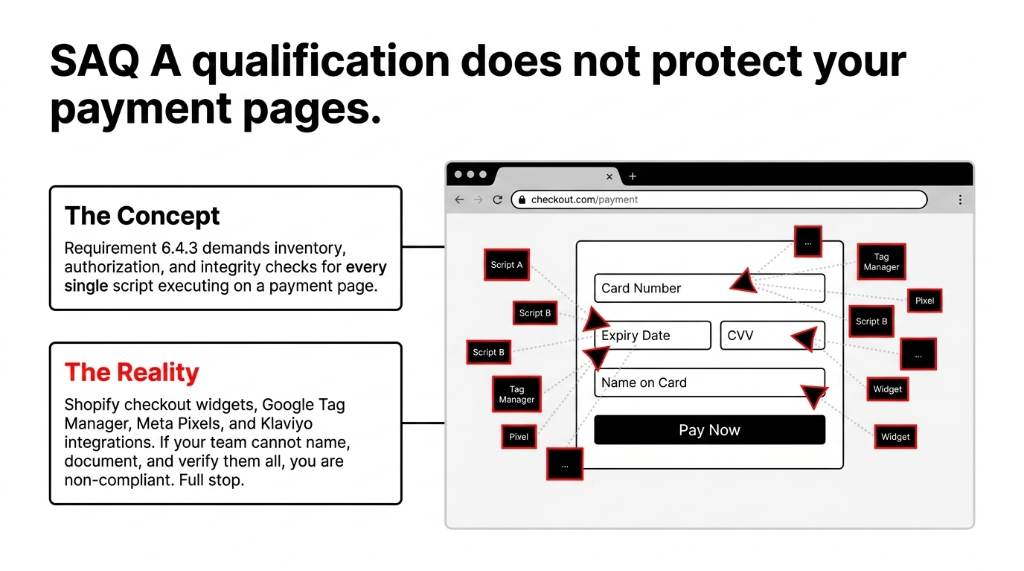
2. Requirement 6.4.3 — Payment Page Script Inventory
Every JavaScript loaded on your payment page must be inventoried, authorized, and integrity-checked. If you are running a Shopify store with a third-party checkout widget and three marketing pixels, you have at minimum four scripts to document.
3. Requirement 11.6.1 — Change and Tamper Detection
You need a mechanism to detect unauthorized changes to HTTP headers and payment page content. This is not just log monitoring — it is a specific detection control for Magecart-style skimming attacks. Very few WAF configurations out of the box cover this.
4. Requirement 5.4.1 — Anti-Phishing (DMARC)
DMARC at reject policy, not just monitor. That means your p=none DMARC record — which most organizations set and forgot — does not qualify. You need p=reject, aligned SPF, and DKIM across every domain that touches cardholder communications.
5. Requirement 12.3.2 — Targeted Risk Analysis
For any control where you chose the frequency of implementation, you now need a documented Targeted Risk Analysis (TRA). This is not a general risk assessment. It is a specific, per-control document proving you evaluated frequency based on threat likelihood.
6. Requirement 3.3.3 — SAD Storage Post-Authorization
Sensitive Authentication Data — full magnetic stripe data, CAV2/CVC2 values, PINs — cannot be stored after authorization, even encrypted. If your legacy transaction processor caches this data "temporarily," it is a direct violation.
ABM Lens: Gap Analysis by Organization Type
Hospitality (Enterprise)
A multinational hospitality company with 3,500 network devices and a recent acquisition achieved 100% automated PCI-DSS compliance reports after implementing automated network security policy management.
Quarterly audits became verification exercises, not firefighting sessions. Scaling to 10,000 devices.
Financial Services (Mid-Market)
A leading U.S. bank implemented tokenization and encryption upgrades that reduced data breach exposure by 58% and eliminated two entire attack vector categories — brute-force and man-in-the-middle.
Average payment card breach in 2024: $4.88M (IBM). Every dollar of v4.0 remediation replaces that liability.
SaaS / E-Commerce
SAQ A qualification does not exempt you from Req 6.4.3 script inventory. If you use Klaviyo, Google Tag Manager, or Meta Pixel on a page that accepts card data, you have a documentation obligation.
Full stop.
How to Actually Map v4.0 in 30 Days
Most QSAs will tell you v4.0 mapping takes 3 to 6 months. That is a billable hours problem, not a complexity problem.
Week 1: Scope the CDE, Digitally
Map every system component that stores, processes, or transmits cardholder data. Include containers, serverless functions, third-party APIs that touch PANs. Export as a living asset register, not a Confluence page nobody updates.
Week 2: Gap Against 64 New Requirements
Use the PCI SSC's official Summary of Changes as your checklist. Assign each requirement a status: Compliant / Partial / Non-Compliant. "We think we do this" is not evidence.
Week 3: Prioritize by Penalty Exposure
MFA gaps (Req. 8), script inventory gaps (Req. 6.4.3), and SAD storage gaps (Req. 3.3.3) are flagged immediately by card brands. Fix those first. DMARC and TRA documentation gaps can run parallel.
Week 4: Execute, Document, Evidence
Remediate and document as you go. The v4.0 audit requires documented proof that controls were implemented intentionally, with a rationale. Especially for Targeted Risk Analyses.
The Controversial Truth Most QSAs Won't Tell You
Most QSAs are still operating mental models built on v3.2.1. We have seen QSA firms assess Requirement 12.3.2 (Targeted Risk Analysis) as N/A for clients who absolutely needed it — because the QSA didn't understand the applicability trigger.
If your QSA cannot explain the difference between the Defined Approach and the Customized Approach without looking it up, find a different QSA.
What Braincuber Can Do for You Right Now
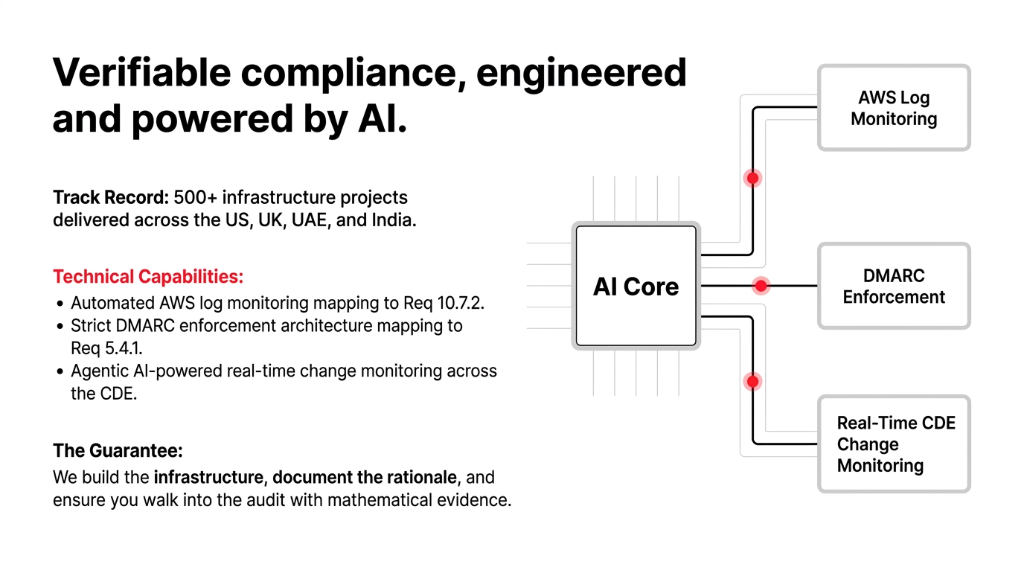
We are an AI-first technology partner with 500+ compliance-adjacent infrastructure projects delivered across the US, UK, UAE, and India. We do not just tell you what is broken. We help you build the detection controls, access management layers, automated monitoring pipelines, and cloud security postures that make PCI-DSS v4.0 a verifiable state rather than a quarterly checkbox.
Whether it is automated log monitoring on AWS that satisfies Req. 10.7.2, DMARC enforcement setup that covers Req. 5.4.1, or a full Agentic AI-powered compliance monitoring layer that flags CDE changes in real time — we build it, document it, and help you walk into your QSA audit with evidence, not hope.
The Braincuber Challenge
Ask your security team one question: "Can you show me the documented Targeted Risk Analysis for every control where we chose implementation frequency?"
If the answer is silence, you have a gap. We can find the other ones in 15 minutes.
Stop Waiting for a Breach to Force the Conversation
Book our free 15-Minute Compliance Readiness Call. We'll identify your top 3 PCI-DSS v4.0 gaps in the first conversation.
Book Your Free Compliance CallFrequently Asked Questions
Is PCI-DSS v4.0 really mandatory now, or is there still a grace period?
Fully mandatory. As of March 31, 2025, all 64 new requirements — previously labeled future-dated best practices — are now enforceable. PCI DSS v4.0.1 is the only active standard. There are no remaining grace periods for any requirement.
What is the difference between the Defined Approach and the Customized Approach?
The Defined Approach means you implement controls exactly as the standard prescribes. The Customized Approach lets you design your own control as long as you can prove it meets the stated security objective — useful for cloud-native, containerized, or serverless CDE architectures.
Does PCI-DSS v4.0 apply if we use a third-party payment processor?
Yes, but scope may be reduced. If your payment page loads scripts from third parties (even analytics or marketing tools), Requirement 6.4.3 requires you to inventory and integrity-check every script on that page. SAQ A qualification does not exempt you.
What happens if found non-compliant after March 31, 2025?
Card brand fines start at $5,000/month for smaller merchants and can reach $100,000/month for Level 1 merchants. A confirmed breach under non-compliance can result in card processing privileges being revoked — effectively ending payment operations.
What is a Targeted Risk Analysis (TRA) and do we need one?
A TRA is a per-control documented analysis justifying why you chose a specific frequency for any v4.0 requirement that allows organizational discretion. Requirement 12.3.2 mandates it. If you run vulnerability scans monthly instead of weekly, you need a TRA documenting that decision.

