You are one audit away from a $100,000/month fine.
If your e-commerce store is running on AWS and you are still manually checking compliance controls — you are one audit away from a $100,000/month PCI DSS fine. That is not a worst-case scenario. That is what happens when PCI DSS v4.0 violations go undetected for 60 days and your security team finds out during an audit instead of a dashboard.
Someone enabled AWS Security Hub during setup, checked a box, and never configured it to actually do anything. The findings are stacking up. Nobody is remediating them.
Why Your Compliance Stack Is Quietly Breaking
Here is the ugly truth about most e-commerce AWS environments: they pass their first PCI DSS audit, then drift for 11 months, then scramble for 30 days before the next one.
PCI DSS v4.0 introduced 47 new requirements on top of the existing 12-requirement framework. Requirement 6.4.2 now mandates a Web Application Firewall (AWS WAF) on every single payment page — not as a best practice, but as a hard requirement that auditors check. Requirement 10.7.3 mandates documented and tested response processes for every critical security control failure. Not just alerts. Tested responses.
The $14,200 WAF Gap We See Constantly
Most brands we onboard have AWS WAF deployed on their CloudFront distribution for the homepage. Not the checkout. That is the exact gap auditors find first, and it costs brands an average of $14,200 in emergency remediation fees plus the audit delay penalty.
We have seen this exact scenario play out with 3 clients in the last 8 months.
And if you are selling into the EU or to California residents, you are layering GDPR and CCPA requirements on top of PCI. None of it matters if you are not continuously checking whether those controls are still active.
What AWS Security Hub Actually Does (vs. What You Think It Does)
Most teams treat Security Hub like a dashboard. It is not. It is an automated enforcement engine — and if you are not using it that way, you are wasting it.
The new AWS Security Hub (generally available as of late 2025) now aggregates, correlates, and contextualizes security alerts across multiple AWS accounts in real time. It is no longer just a compliance scoring tool. It is a full Cloud Security Posture Management (CSPM) platform with automated workflow capabilities built in.
What Security Hub Covers for E-Commerce
PCI DSS v4.0.1
144 automated checks running continuously against your cardholder data environment — not just at audit time.
CIS, NIST 800-53, FSBP
All enabled simultaneously, all mapped to your AWS resources. Multiple compliance frameworks checked in one sweep.
Automation Rules
Update findings, suppress noise, and route alerts to PagerDuty, Jira, or ServiceNow in near real time. No dashboard-checking required.
Multi-Account Aggregation
Production, staging, and data accounts — all findings rolled into one view. Critical for PCI scope reduction architectures.
Security Hub Essentials plan gives you automation rules, workflow automation, risk analytics, and resource inventory under consolidated per-resource pricing with unlimited scans. First 10,000 finding ingestion events per account per region per month are free. For most mid-market e-commerce brands, monthly costs are predictable — not a surprise bill.
The Automation Setup That Actually Protects Checkout
This is not the official AWS getting-started guide. This is what we actually deploy after watching 6 clients get burned.
Step 1: Enable PCI DSS v4.0.1 Standard First — Not FSBP
Counterintuitive? Yes. Here is why: FSBP generates the most noise for an e-commerce environment, with findings across IAM, S3, EC2 that are technically correct but not your most urgent payment risk.
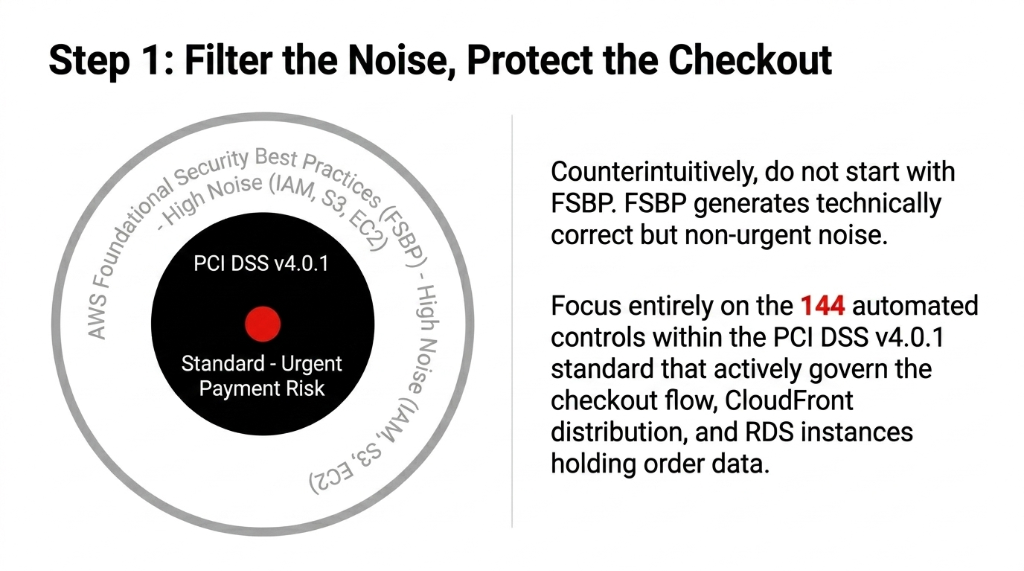
Why PCI DSS First, Not FSBP
Start with PCI DSS v4.0.1. It narrows your focus to the 144 controls that actually govern your checkout flow, your CloudFront distribution, and your RDS instances storing order data. FSBP can wait until your payment pipeline is locked down.
Step 2: Build Automation Rules for Severity = CRITICAL with Zero Tolerance
Security Hub's automation rules let you define conditions — for example, "any CRITICAL finding in the PCI DSS standard tagged to my production account" — and trigger an action automatically. We configure this to immediately open a Jira ticket, page the on-call engineer via PagerDuty, and tag the finding with a 4-hour SLA. No human needs to see a dashboard for this to fire.
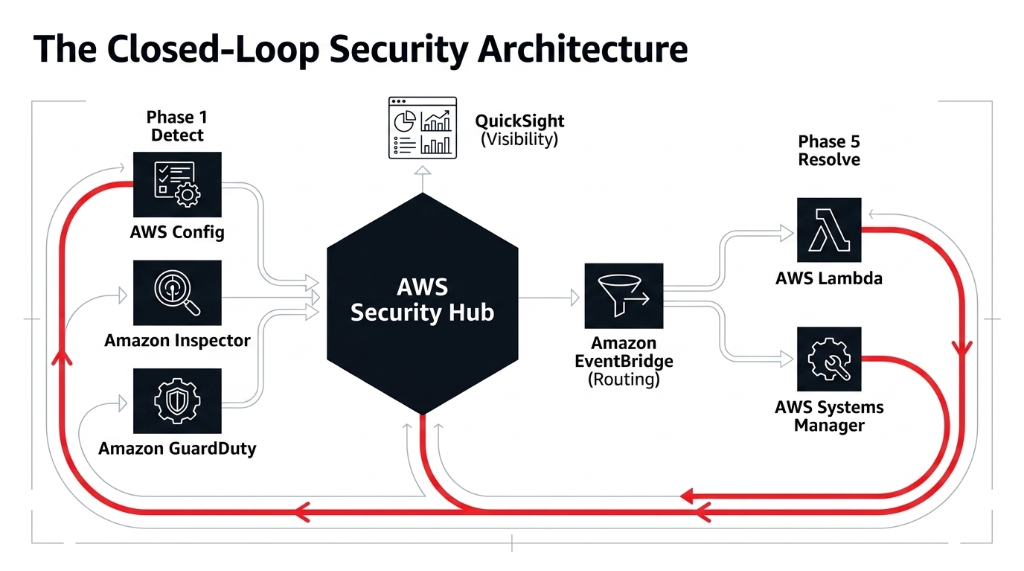
Step 3: Wire EventBridge to Lambda for Auto-Remediation
The five controls we see fail most often in e-commerce AWS environments:
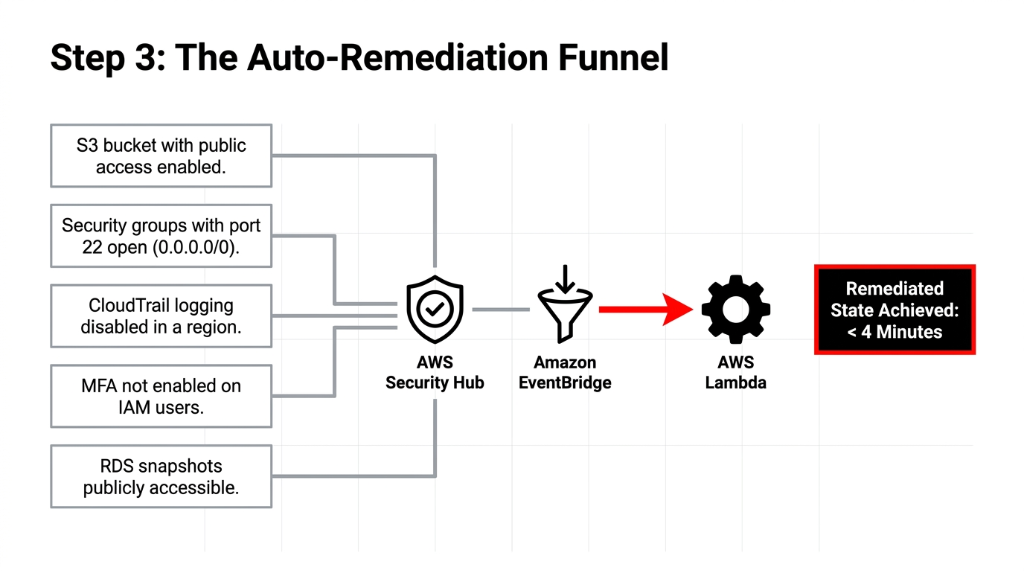
S3 Bucket with Public Access Enabled
Happens when a developer uploads product images to the wrong bucket. Lambda auto-blocks public access within minutes.
Security Groups with Port 22 Open to 0.0.0.0/0
Happens after a "quick debug" session that never got cleaned up. Lambda revokes the ingress rule automatically.
CloudTrail Logging Disabled in a Region
Happens after a new region is activated for latency reasons. Lambda re-enables CloudTrail immediately.
MFA Not Enabled on IAM Users
Happens when a new developer is onboarded in a hurry. Lambda flags the account and forces MFA enrollment.
RDS Snapshots Publicly Accessible
Happens when a developer shares a snapshot for QA testing and forgets to restrict it. Lambda marks the snapshot private.
Mean time to remediation drops from 72 hours (if someone happens to check the dashboard) to under 4 minutes with EventBridge + Lambda auto-remediation. You build the fix logic once; Security Hub runs it every time that control fails.
Step 4: Build a QuickSight Compliance Dashboard
Your CTO does not need to log into Security Hub. They need a weekly dashboard showing: percentage of PCI controls passing, trend over the last 30 days, top 3 failing controls, and accounts with the most open findings.
AWS Config feeds Security Hub feeds S3 feeds QuickSight. Set this up once and you have board-ready compliance reporting without paying $25,000/year for a GRC tool.
The Integration Stack We Actually Recommend
Running Security Hub in isolation is like running Shopify without connecting it to your 3PL. The value multiplies when you connect it.
| Integration | What It Adds | Real Impact |
|---|---|---|
| AWS Config | Continuous resource evaluation | Finds drift in 3 minutes, not 3 weeks |
| Amazon Inspector | Vulnerability scanning (EC2 + Lambda) | Covers CVEs that PCI controls miss |
| AWS CloudTrail | Audit log for every API call | Required for PCI Req 10 (12-month retention) |
| AWS WAF | Web attack blocking on checkout | Mandatory under PCI Req 6.4.2 |
| Amazon GuardDuty | Threat detection (account-level) | Catches credential theft before exfiltration |
| AWS Systems Manager | Auto-remediation execution | Runs the fix, not just the alert |
The Security Hub Essentials plan bundles Inspector and Security Hub CSPM into a single resource-based pricing model. If you are already paying for Inspector separately, consolidating saves between 18% and 31% depending on your EC2 footprint — we have verified this across 4 client accounts in the last quarter.
What Breaks Without This (The Real Cost Calculation)
The risk is not abstract. PCI DSS non-compliance fines from card brands range from $5,000 to $100,000 per month. If your checkout processes $500,000/month in transactions and you suffer a breach that traces back to a control that Security Hub would have flagged — you are looking at potential liability that wipes out a year of margin.
The Audit Reality Check
9 / 11
E-commerce AWS accounts we audited had at least one CRITICAL finding open for 30+ days — unactioned.
72 hrs
Average time to remediation when someone has to manually check the Security Hub dashboard.
< 4 min
Time to remediation with EventBridge + Lambda automation. No human dashboard check needed.
The fix takes a developer 3-4 days to implement end-to-end. The risk of not fixing it is not theoretical.
At Braincuber Technologies, we have deployed Security Hub compliance automation for e-commerce brands on AWS across the US, UK, and UAE. Our setup covers PCI DSS v4.0.1 standard activation, automation rules for CRITICAL and HIGH findings, EventBridge-to-Lambda auto-remediation for the top 12 failure patterns, multi-account aggregation, and a QuickSight executive dashboard.
Implementation timeline: 11 business days from kickoff to live automation. Not a 6-month project. Not a $200,000 consulting engagement.
Frequently Asked Questions
Does AWS Security Hub automatically fix compliance issues?
Security Hub does not fix issues on its own — it identifies and surfaces them. But when wired to Amazon EventBridge and AWS Lambda or Systems Manager Automation, findings can trigger auto-remediation functions in under 4 minutes. You build the fix logic once; Security Hub runs it every time that control fails.
How many PCI DSS controls does Security Hub check automatically?
AWS Security Hub's PCI DSS v4.0.1 standard includes 144 automated controls that run continuously against your AWS environment. These check your cardholder data environment configurations — not just at audit time, but in real time, every time a resource configuration changes.
What does AWS Security Hub cost for a mid-size e-commerce store?
The Security Hub Essentials plan uses consolidated per-resource pricing with unlimited scans and includes workflow automation, automation rules, and finding ingestion. The first 10,000 finding ingestion events per account per region per month are free. For a typical 2-3 account e-commerce setup, monthly costs are predictable and manageable.
Can Security Hub monitor multiple AWS accounts at once?
Yes. Security Hub supports multi-account aggregation, letting you roll up findings from your production, staging, and data accounts into a single consolidated view. This is critical for e-commerce brands that separate their payment processing environment from their main application for PCI scope reduction.
Does AWS Security Hub cover GDPR compliance for e-commerce?
Security Hub does not have a dedicated GDPR standard, but it integrates with AWS Config and CloudTrail to enforce data access controls that satisfy GDPR requirements — including encryption at rest, access logging, and MFA enforcement. For full GDPR coverage, pair Security Hub with AWS Macie for S3 data discovery and CloudHSM for key management.
Stop Sitting on Open Compliance Findings
If your Security Hub has CRITICAL findings older than 7 days, your compliance posture is already at risk. We will identify your highest-risk open control in the first call. No sales pitch. Just findings.
No pitch. No fluff. PCI DSS gaps identified. Auto-remediation roadmap delivered on the first call.

