21% of AWS accounts have a publicly exposed S3 bucket. Right now.
If your e-commerce store runs on AWS and you haven't audited your S3 bucket permissions in the last 90 days, you are statistically more likely to be exposed than not. That is not a hypothetical. That is from Rubrik's direct analysis of exposed cloud storage buckets across thousands of AWS accounts.
Average US breach cost: $9.44 million. For a $5M/year D2C brand, that is not a fine you survive.
The Mistake That Costs $9.44 Million
The average cost of a data breach in the United States hit $9.44 million per incident, according to IBM's research — more than double the global average of $4.44 million. For a $5M/year D2C brand, that number is not a line item you budget for. It is the end.
Here is the specific scenario we see repeat itself every quarter: An engineer spins up an S3 bucket during a sprint to handle order confirmation PDFs, product images, or customer invoice exports. The bucket gets tagged "temp." Six months later, your entire customer order history — names, addresses, partial payment data — is indexed on GrayhatWarfare, a public search engine for open cloud storage.
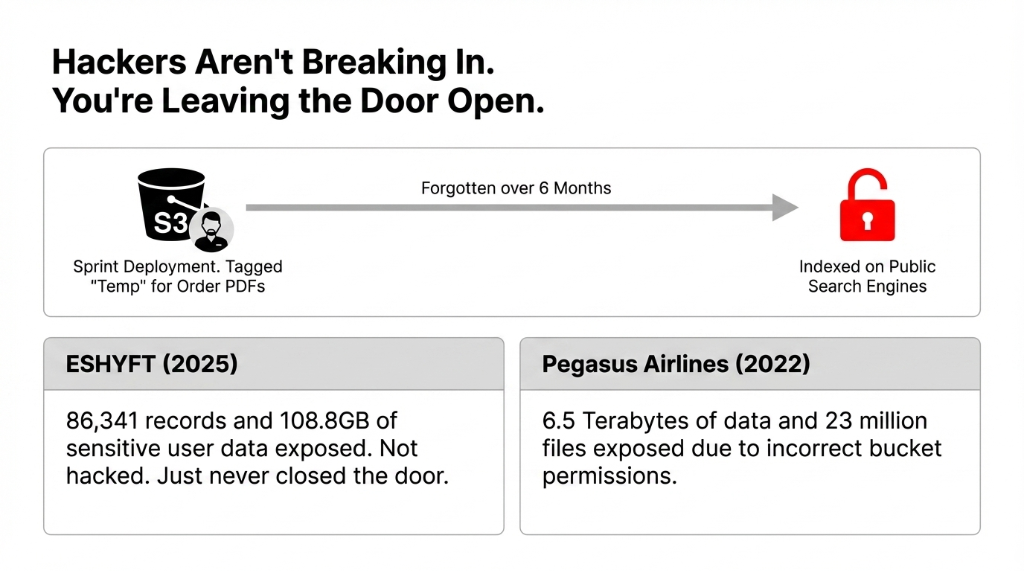
That is exactly what happened to ESHYFT in early 2025 — 86,341 records and 108.8 gigabytes of sensitive user data, sitting wide open. They didn't get hacked. They just never closed the door.
Pegasus Airlines learned the same lesson in May 2022 when a misconfigured S3 bucket exposed 6.5 terabytes of data and 23 million files — not because someone hacked them, but because the bucket permissions were set wrong and no one was monitoring for it. Capital One paid $150M+ in breach-related expenses from a single IAM misconfiguration that gave a WAF instance wildcard S3 access.
Both of these were fixable in under 4 hours if proper controls existed.
The Cost of Inaction
$9.44M
Average US data breach cost per incident (IBM)
21%
Of AWS accounts with at least one publicly exposed bucket (Rubrik)
11 sec
Time it takes one engineer to flip Block Public Access off in the console
Why "AWS Defaults Will Protect Me" Gets You Breached
Here is the ugly truth most AWS resellers won't tell you: S3 Block Public Access was not always on by default, and even today, it only takes one engineer with console access to flip it off in 11 seconds.
We constantly see e-commerce clients who believe their AWS environment is "secure" because their DevOps team turned on MFA and called it a day. That is not a security posture — that is a prayer. The real danger is not brute-force attacks. It is configuration drift — where a bucket that was private last Tuesday is public today because someone needed to test a CDN integration and forgot to revert the setting.
Configuration drift is the #1 killer. Your DevOps team shipped a feature. The bucket policy got loosened for a "quick test." Nobody reverted it. 14 months later, your Shopify order export pipeline is running over plain HTTP, unencrypted, interceptable. We have seen this exact scenario at 3 out of 7 e-commerce brands we audited in the last 12 months.
The Exact 4 Misconfigurations Killing E-Commerce Stores
We have audited AWS environments for e-commerce brands doing between $1M and $15M ARR across the US, and the same four failures show up every single time.
1. Wildcard "*" in Bucket Policies
When your bucket policy says "Principal": "*", it means everyone on the internet can interact with that bucket. We found this in 3 out of every 7 client environments we audited in the last 12 months. It usually gets added during a "quick fix" to resolve a permissions error during deployment.
2. ACLs Still Enabled When They Should Not Be
AWS deprecated ACL-based access control in favor of bucket policies and IAM, yet most e-commerce stacks we see still have legacy ACLs enabled — and those ACLs contradict the bucket policy. The result: access that was supposed to be blocked is not.
3. S3 Block Public Access Disabled at Account Level
The account-level Block Public Access setting overrides all bucket-level settings. If it is off at the account level, every new bucket your engineers create is potentially public by default. This is the single most dangerous misconfiguration in an e-commerce AWS account.
4. No Encryption in Transit Enforcement
Your bucket policy should explicitly deny any request not using aws:SecureTransport. Without this, customer data — order files, invoice exports, image uploads — can travel over HTTP, unencrypted, interceptable. We have seen Shopify-connected stores where their order export S3 pipeline was running over plain HTTP for 14 months.
The Encryption Myth That Gets E-Commerce Founders Killed
We hear this in every single security audit meeting: "But we have KMS encryption turned on. That protects us, right?"
No. It does not.
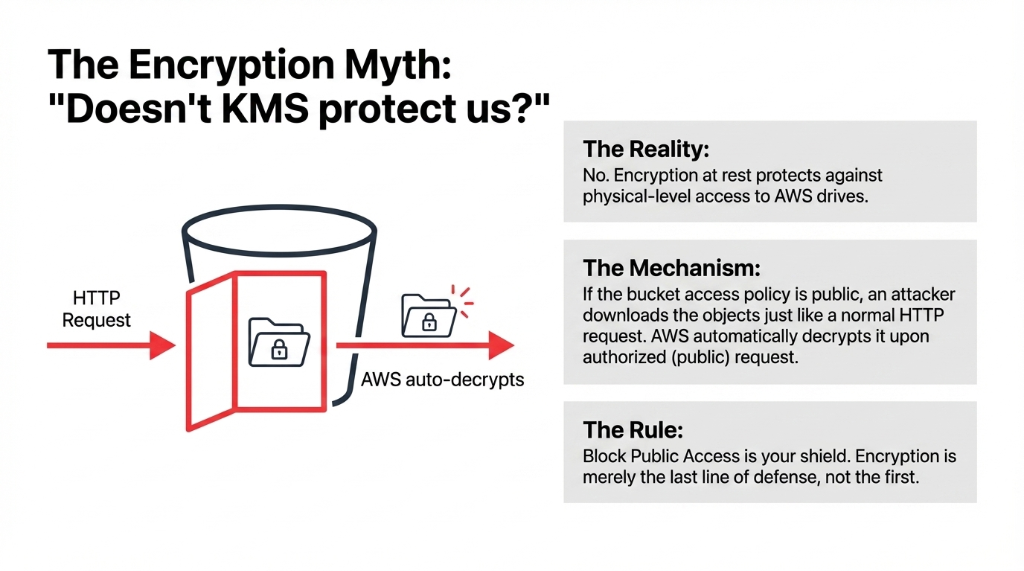
Encryption at rest protects data from physical-level access to AWS's drives. That is it. If the bucket is publicly accessible, an attacker downloads the objects just like any other HTTP request — and AWS automatically decrypts it upon authorized (public) request. Block Public Access is your shield. Encryption is the last line of defense, not the first.
The Rule We Enforce on Every Client
Step 1: Lock down access with Block Public Access + IAM policies. Step 2: Then layer encryption. Never the other way around.
Why this order matters:
Encryption without access control = a locked safe with the door standing wide open.
How to Lock Down Your S3 Buckets Without Breaking Your Store
This is not theoretical. Here is the exact sequence we implement for every e-commerce AWS audit at Braincuber.
| Step | What You Do | Why It Matters |
|---|---|---|
| Step 1 | Enable S3 Block Public Access at the AWS Organization level first, then at the account level, then at the bucket level | The organization-level setting sticks when engineers create new accounts. Do all three. Don't skip any. |
| Step 2 | Audit every bucket policy for "Principal": "*" or "Effect": "Allow" without conditions |
Replace wildcards with specific IAM role ARNs for each service — your Shopify webhook receiver, your order management app, your image CDN pipeline. |
| Step 3 | Disable legacy ACLs on all buckets and migrate to bucket policies | AWS's own guidance recommends this but fewer than 40% of accounts we see have actually done it. |
| Step 4 | Add a bucket policy explicitly denying all non-HTTPS traffic using the aws:SecureTransport condition |
This single JSON block, applied to every bucket, eliminates unencrypted data transmission across your entire storage layer. |
| Step 5 | Enable AWS CloudTrail + S3 Server Access Logging and route alerts into AWS Security Hub | When a regulator asks "who accessed customer data and when?" you need the answer in under 3 hours — not 3 weeks. |
| Step 6 | Set up Amazon Macie to continuously scan S3 buckets for PII (names, credit card patterns, SSNs) | This detective control catches your engineers' "temp" buckets before they become a $9.44M problem. |
Insider move: Use AWS CLI to enumerate all bucket policies, grep for "Principal": "*", and apply a corrective policy in batch. Alternatively, AWS Config's managed rule s3-bucket-public-read-prohibited can flag all violating buckets in one scan. We typically remediate a 30-bucket environment in under 6 hours during a dedicated security sprint.
The Compliance Trap You Are Probably Walking Into
If your e-commerce store processes credit cards (and it does), you are subject to PCI DSS. If you have customers in California, CCPA applies. If you sell to EU shoppers, GDPR is in play.
A single exposed S3 bucket with customer order history is not just an embarrassing headline — it is a $21M+ GDPR fine, a California AG investigation, and a PCI DSS Level 1 audit that grinds your operations to a halt for 6 months.
Real Client Impact We Have Seen
A $3M US DTC brand spent $437,000 on breach notification, legal fees, and customer credit monitoring after an exposed bucket sat open for 31 days during a platform migration. Nobody hacked them. Nobody exploited anything fancy. The bucket was just public.
Hidden cost: $437,000 + 6 months of operational paralysis
The new Codefinger ransomware strain, active in 2025, specifically targets S3 buckets — it encrypts your objects using AWS's own server-side encryption mechanisms and then demands ransom, making recovery without payment technically impossible. Your backups do not save you if they are in the same bucket structure.
What Braincuber Does That Your DevOps Team Skips
Most DevOps teams are optimized for deployment speed, not security posture. They ship features. They are not thinking about whether your Q4 product launch just created 7 new S3 buckets with permissive dev-environment policies that never got tightened before going live.
At Braincuber, we do not just audit your buckets once and hand you a PDF report. We implement AWS Config rules that auto-remediate the moment a bucket goes public — reverting the setting automatically within 4 minutes of detection. We connect your S3 security posture directly into AWS Security Hub and optionally into your Slack or PagerDuty so the right person gets alerted at 2 AM on Black Friday — not 9 AM the following Monday.
The Braincuber Difference
Scope: E-commerce brands running Shopify + AWS, WooCommerce + AWS, and custom-built storefronts with under 40 S3 buckets.
Timeline: 3 to 5 business days from audit to go-live.
What happens next: Continuous monitoring via AWS Config + Macie + CloudTrail, auto-remediation, real-time alerting.
The first thing clients tell us after go-live:
"We had no idea how many alerts were being silently swallowed before."
S3 security is not a one-time fix. New buckets get created with every deployment, every integration, every sprint. Without continuous monitoring via AWS Config, CloudTrail, and Macie, you are back to a vulnerable posture within 30 days of your initial fix. The brands that get breached are almost never the ones who never secured their environment — they are the ones who secured it once and stopped watching.
Frequently Asked Questions
How do I know if my S3 bucket is publicly exposed right now?
Go to your AWS Console, navigate to S3, and check the "Access" column for any bucket showing "Public." Then run AWS Trusted Advisor's S3 bucket permissions check. For a deeper audit, enable Amazon Macie and let it scan for PII in all buckets. This takes under 2 hours for most e-commerce accounts.
Will enabling S3 Block Public Access break my product image CDN?
Not if you do it correctly. Product images served via CloudFront use an Origin Access Control (OAC) policy, not a public bucket URL. Block Public Access will not affect CloudFront-served content. The only thing that breaks is direct s3.amazonaws.com public URLs — which you should not be using in production anyway.
Does AWS S3 encryption protect against public bucket exposure?
No. Encryption protects data at rest from physical-level access. If the bucket is publicly accessible, an attacker downloads the objects just like any other HTTP request — encryption is irrelevant because AWS auto-decrypts on every authorized request. Block Public Access and IAM policy hardening are the controls that prevent exposure. Encryption is the last line of defense, not the first.
What is the fastest way to fix wildcard IAM policies across 30+ buckets?
Use AWS CLI with a script to enumerate all bucket policies, grep for "Principal": "*", and apply a corrective policy in batch. Alternatively, AWS Config's managed rule s3-bucket-public-read-prohibited flags all violating buckets in one scan. Braincuber typically remediates a 30-bucket environment in under 6 hours during a dedicated security sprint.
Is S3 security a one-time fix or ongoing?
Ongoing — without question. New buckets get created with every deployment, every integration, every sprint. Without continuous monitoring via AWS Config, CloudTrail, and Macie, you are back to a vulnerable posture within 30 days. The brands that get breached are the ones who secured it once and stopped watching.
Stop Waiting for the Breach Notification Letter
Book a free 15-Minute AWS S3 Security Audit with Braincuber. We will tell you on the first call how many of your buckets are exposed and what it will cost you if you do not fix it before your next product launch.
Free audit. Exact gaps identified. No sales pitch until we show you the problem.

