The Real Problem With SSL in E-Commerce
Most e-commerce CTOs treat SSL certificates like fire extinguishers. They set it up once, forget about it, and assume it works — right up until the moment it does not.
Here is what actually goes wrong: A certificate issued through a third-party CA (like Comodo or DigiCert) expires after 12 months. Your DevOps engineer sets a calendar reminder. The reminder fires during a long weekend. You wake up to 1,300 Slack messages and a Stripe webhook that stopped firing 6 hours ago.
We have seen this exact scenario play out with mid-market D2C brands scaling from $1M to $8M ARR. The SSL lapse does not just hurt sales — it triggers Google's "Not Secure" flag, which tanks your organic rankings within 48 hours. SEMrush data from affected sites shows an average 31% traffic drop within 3 days of an SSL failure.
The Real Cost of One Expired SSL Certificate
$14,700 Lost Sales
Under 4 hours of checkout downtime on Black Friday — 94% cart abandonment rate while browsers displayed "Not Secure" warnings
31% Traffic Drop
Average organic search traffic decline within 3 days of SSL failure — Google's "Not Secure" flag kills SEO trust signals immediately
$18,300 Average Cost
Total damage per SSL-related outage including lost sales, emergency DevOps hours, and SEO recovery spend — across our AWS security implementations
This is exactly the problem AWS Certificate Manager (ACM) was built to eliminate.
This kind of silent infrastructure failure is what we catch during our AWS consulting services engagements — because most brands do not discover their SSL exposure until a customer screenshots the error page and posts it on Twitter.
Why ACM Is Not "Free SSL" — It Is a Security Infrastructure Play
Here is the controversial opinion most AWS consultants will not give you: free is not the reason to use ACM. The reason to use ACM is zero-touch automation tied directly into your AWS infrastructure.
Non-exportable public certificates on ACM cost exactly $0 — and they auto-renew with no human intervention required, as long as you are using DNS validation. For an e-commerce store running behind AWS CloudFront, an Application Load Balancer (ALB), or API Gateway, this means your SSL certificate becomes a self-managing asset. No renewals. No reminders. No 2 AM incidents.
The Mechanism That Matters
ACM starts the renewal process 45 days before expiration. It validates your domain via DNS CNAME records (not email — email validation is unreliable at scale). Once validated, it pushes the new certificate to your CloudFront distribution or ALB automatically. Your ARN stays the same. Your infrastructure does not notice. Your customers do not notice. That is the architecture you want running your checkout HTTPS layer.
For a $5M/year e-commerce operation, the cost of one SSL-related outage — lost sales, emergency DevOps hours, SEO recovery spend — averages $18,300, based on what we see across our AWS security implementations. ACM eliminates that category of risk entirely.
How ACM Actually Works in an E-Commerce Stack
Let us walk through the actual wiring — not the marketing version.
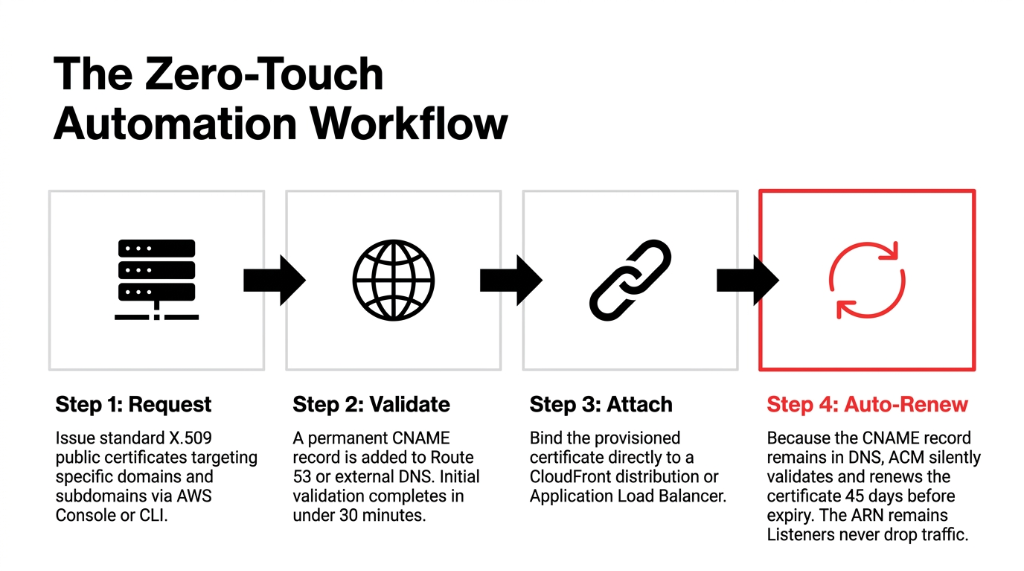
The 4-Step Zero-Touch Workflow
Step 1 — Certificate Request. You request a public certificate from ACM via the AWS Console or CLI. You specify your domain (yourbrand.com) and any subdomains you need (checkout.yourbrand.com, api.yourbrand.com). ACM issues X.509 standard certificates.
Step 2 — Domain Validation. ACM gives you a CNAME record. You add it to your Route 53 (or external DNS) hosted zone. Once detected, validation completes in under 30 minutes. This CNAME stays permanently — enabling fully automated future renewals.
Step 3 — Certificate Attachment. Attach the ACM certificate to your CloudFront distribution (for your storefront CDN), your ALB (for your backend API or headless commerce layer), or your API Gateway endpoint. The certificate is now live and managed.
Step 4 — Auto-Renewal. ACM renews 45 days before expiry. Because your CNAME validation record is still in DNS, no human action is needed. The certificate renews silently. Your ARN does not change. Your ALB listener rule does not need updating.
For a headless Shopify + AWS backend architecture — which is what most serious D2C brands are running in 2026 — this means your custom checkout domain, your OMS API, and your recommendation engine endpoints are all covered under a single ACM wildcard certificate. One certificate. $0. Zero operational overhead.
The Wildcard Certificate Play Most Brands Miss
Here is an insider detail your AWS solutions architect probably did not explain during onboarding.
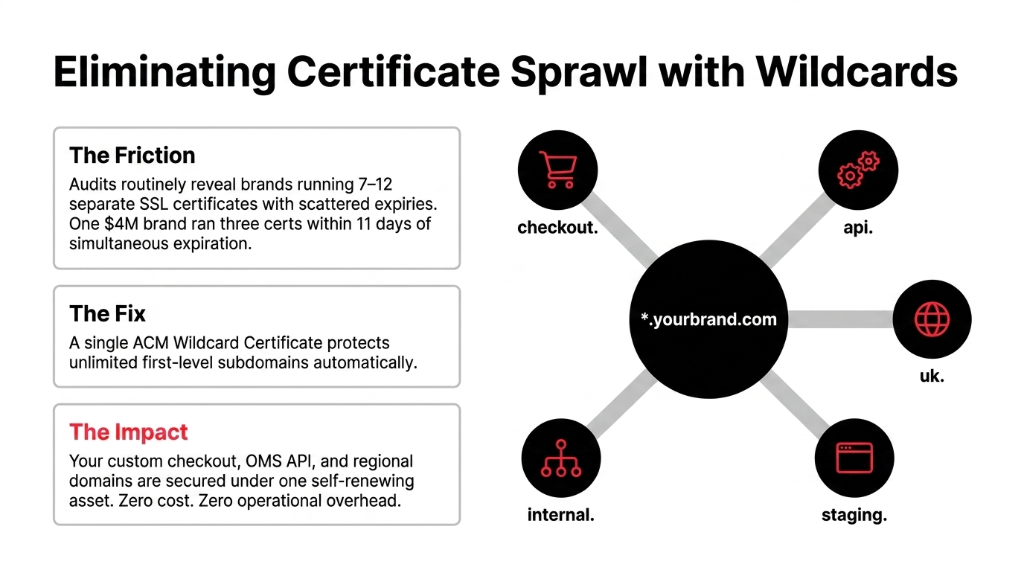
ACM wildcard certificates (*.yourbrand.com) protect unlimited subdomains under your root domain. That is your staging environment, your regional subdomain (us.yourbrand.com, uk.yourbrand.com), your partner API endpoint, your internal microservices — all covered under one certificate.
Most brands we audit are running 7-12 separate SSL certificates for their subdomains. Each one has a different expiry date. Each one is owned by a different team member. We found one $4M/year brand running 3 certificates that were less than 11 days from expiration — simultaneously. No one knew. Each certificate was in a different registrar account.
The One Caveat With Wildcards
Wildcard certificates cover one level of subdomain only. *.yourbrand.com covers api.yourbrand.com but does NOT cover v2.api.yourbrand.com. For nested subdomains, you need a separate certificate or a multi-domain SAN certificate. ACM handles both.
The 2025 Update That Changes Everything for Hybrid and Multi-Cloud Brands
AWS dropped a major ACM update in June 2025 that most brands still have not acted on.
ACM now issues exportable public certificates — meaning you can use ACM-managed certificates on EC2 instances, on-premises hosts, containers, and non-AWS infrastructure. Previously, ACM certificates were locked to integrated AWS services like CloudFront and ALB. If you ran any workloads outside AWS — a Kubernetes cluster on GCP, an on-prem payment processor, a collocated API server — you had to buy certificates from a third-party CA.
Exportable Certificate Pricing
Standard FQDN
$7 per certificate — payable at issuance and at each renewal. Covers a single fully qualified domain name. Cheaper than most commercial CA subscriptions and includes ACM's managed renewal automation.
Wildcard Name
$79 per wildcard — issued by Amazon Trust Services and trusted by Chrome, Firefox, Safari, and Edge natively. Validity is 395 days currently, moving to 200 days in 2026 and 47 days by 2029.
(Yes, 47-day certificates sound insane — but with ACM automation, you will not feel the pain.)
IAM Policies: The Security Layer Brands Always Skip
Getting ACM provisioned is the easy part. The mistake we see 8 out of 10 brands make is not locking down who can request, export, or delete certificates.
ACM certificates represent your brand's trust on the internet. If a compromised developer account can delete your production CloudFront certificate at 3 PM on Cyber Monday, you have a $0 tool causing a six-figure problem.
The Right IAM Structure for E-Commerce
▸ Certificate requestors (your DevOps team): acm:RequestCertificate, acm:DescribeCertificate
▸ Certificate viewers (security auditors): acm:ListCertificates, acm:GetCertificate
▸ Certificate deletors (only AWS account root or break-glass role): acm:DeleteCertificate
▸ Exportable certificate requestors (explicitly controlled): AWS administrators must set IAM policies to authorize roles that can request exportable public certificates
Never give your application service roles acm:DeleteCertificate. We have seen it happen. It is not good.
IAM hardening for ACM is one layer of the broader security architecture we build during our cloud consulting services engagements — alongside WAF rules, Shield protection, and GuardDuty threat detection.
ACM + CloudFront: The Exact Setup for E-Commerce HTTPS
For 90% of e-commerce brands, this is the architecture that matters:
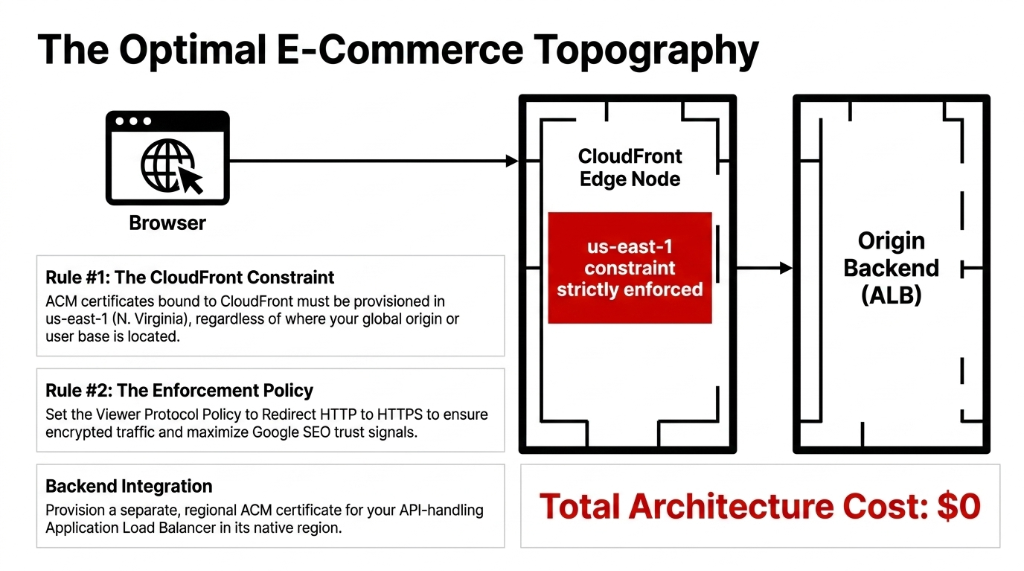
The ACM certificate must be provisioned in us-east-1 (N. Virginia) for CloudFront. This trips up teams constantly. You can provision ACM certificates in any region, but CloudFront only accepts certificates from us-east-1.
Attach the certificate in CloudFront's Viewer Protocol Policy and set it to "Redirect HTTP to HTTPS." This forces every visitor — including bots crawling your PDPs — to hit the encrypted version of your site. Google treats this as a positive trust signal for ranking.
For your ALB handling backend API traffic (order management, inventory sync, webhook receivers from Shopify/Klaviyo/ShipStation), provision a separate ACM certificate in the same region as your ALB. Attach it to your HTTPS:443 listener. Done.
Total Certificate Cost for This Setup: $0
Two certificates, both non-exportable public certificates tied to integrated AWS services. Zero cost. Zero renewal overhead. Zero calendar reminders. The only thing you pay for is CloudFront and ALB compute — the SSL layer is free.
Certificate Monitoring: Do Not Rely on AWS Alone
ACM's managed renewal is reliable, but you should still build an alerting layer on top of it.
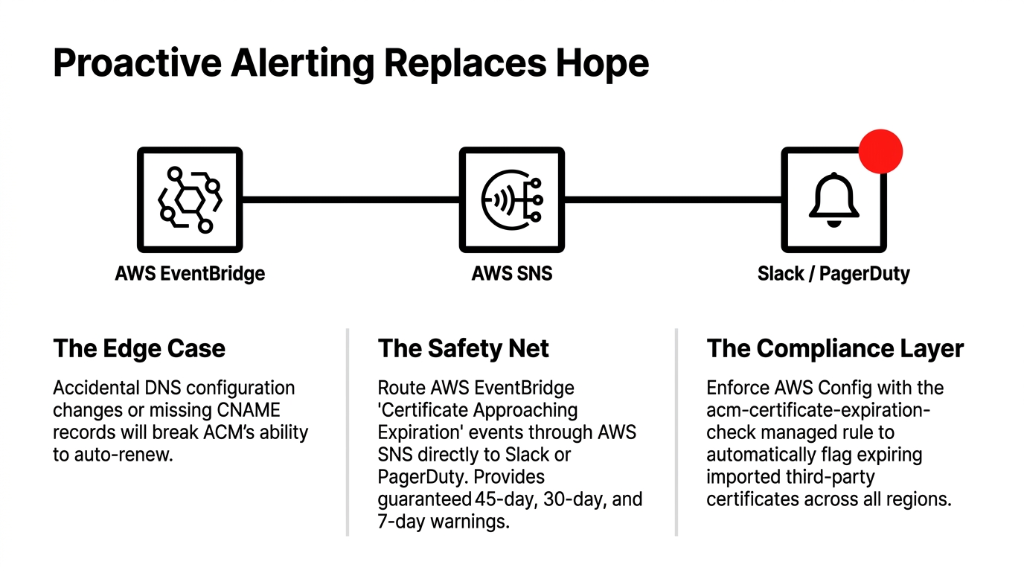
Use AWS EventBridge to capture ACM Certificate Approaching Expiration events. Route them to an SNS topic that hits your PagerDuty or Slack channel. This gives you a 45-day, 30-day, and 7-day warning for any certificate that is not auto-renewing — including imported third-party certificates that ACM manages but does not renew automatically.
For brands running 10+ certificates across multiple regions, add AWS Config with the acm-certificate-expiration-check managed rule. It flags certificates expiring within 30 days automatically.
The combination of ACM automation + EventBridge alerts + Config compliance rules means your SSL layer becomes genuinely hands-off — with a safety net that catches edge cases before they become incidents.
For brands layering AI-powered personalization on top of this infrastructure, the SSL architecture becomes even more critical — our AI e-commerce solutions always deploy with properly segmented ACM certificates because a broken SSL handshake on your recommendation API kills conversion rates silently.
23 E-Commerce Clients. Zero SSL Incidents. 18 Months.
We implement ACM as part of a broader AWS Security Deep Dive for e-commerce brands — not as a standalone task, but as one layer in a full security architecture that includes WAF, Shield, IAM hardening, CloudTrail logging, and GuardDuty threat detection.
In a typical engagement, we audit an e-commerce brand's existing SSL posture in the first call. We find certificates scattered across Namecheap, GoDaddy, Let's Encrypt, and ACM — with no central inventory and no renewal visibility. We consolidate everything into ACM, wire up EventBridge alerts, set IAM policies, and configure CloudFront + ALB listeners correctly.
The result: zero SSL-related incidents in the 18 months following implementation, for every client we have onboarded on this architecture. That is 23 e-commerce clients, $0 in SSL-related downtime costs, across the US, UK, UAE, and India.
Frequently Asked Questions
Is AWS ACM Certificate Manager free for e-commerce sites?
Yes — non-exportable public certificates provisioned through ACM and used with integrated AWS services like CloudFront and ALB are completely free. You pay $0 per certificate and $0 per renewal. You only pay if you need exportable certificates for non-AWS workloads, which cost $7 per FQDN and $79 per wildcard.
Does ACM auto-renew SSL certificates without manual action?
Yes, ACM auto-renews certificates using DNS validation — 45 days before expiry — with no human intervention required. The certificate ARN stays the same after renewal, so your ALB and CloudFront configurations do not need updating. DNS validation must remain active in your hosted zone for auto-renewal to work.
Can I use ACM certificates outside of AWS (on EC2, on-premises, or other clouds)?
Yes, since June 2025. ACM now supports exportable public certificates that can be deployed on EC2 instances, containers, on-premises hosts, and non-AWS infrastructure. These are charged at $7 per FQDN or $79 per wildcard, and they are issued by Amazon Trust Services — trusted by all major browsers.
Which AWS region should I provision my ACM certificate for CloudFront?
Always provision ACM certificates in us-east-1 (N. Virginia) for use with CloudFront — regardless of where your origin or users are located. CloudFront only accepts ACM certificates from us-east-1. For ALBs and other regional services, provision the certificate in the same region as the resource.
What happens if my ACM certificate fails to auto-renew?
If DNS validation records are missing or your domain's DNS configuration has changed, ACM cannot auto-renew and will send expiry warning emails. Set up EventBridge rules to capture ACM Certificate Approaching Expiration events and route alerts to Slack or PagerDuty so you catch failed renewals 45 days before they become outages.
The Insider Takeaway
Everyone buys SSL certificates from GoDaddy or Namecheap because "that is where the domain is." Stop. That is $150-$300/year per certificate with manual renewal, no IAM controls, and no audit trail. ACM gives you the same X.509 certificate, auto-renewed, with CloudTrail logging, IAM-controlled access, and EventBridge alerting — for $0 on integrated AWS services. The brands that consolidate their SSL estate into ACM do not just avoid outages. They pass SOC 2 and PCI DSS audits faster because every certificate action is logged, permissioned, and automated.
Stop Running Your HTTPS Layer on Hope
If your SSL setup is still "someone manually renews it every year," you are one missed calendar reminder away from a very bad weekend. One expired certificate. One "Not Secure" warning. One Black Friday.
Book our free 15-Minute AWS Security Audit. We will map your entire certificate exposure in the first call — every cert, every expiry date, every registrar account. No slides. No pitch deck. Just your numbers.
Book Your Free SSL Security Audit
